5 Reasons Why Businesses Need Ethical Hackers
5 Reasons Services Need Honest Cyberpunks
Hacking, which has belonged of calculating for over 50 years, is an extremely wide self-control, which covers a variety of subjects. The very first reported hacking was in 1960 at MIT and also the term ‘Hacker’ was made use of.
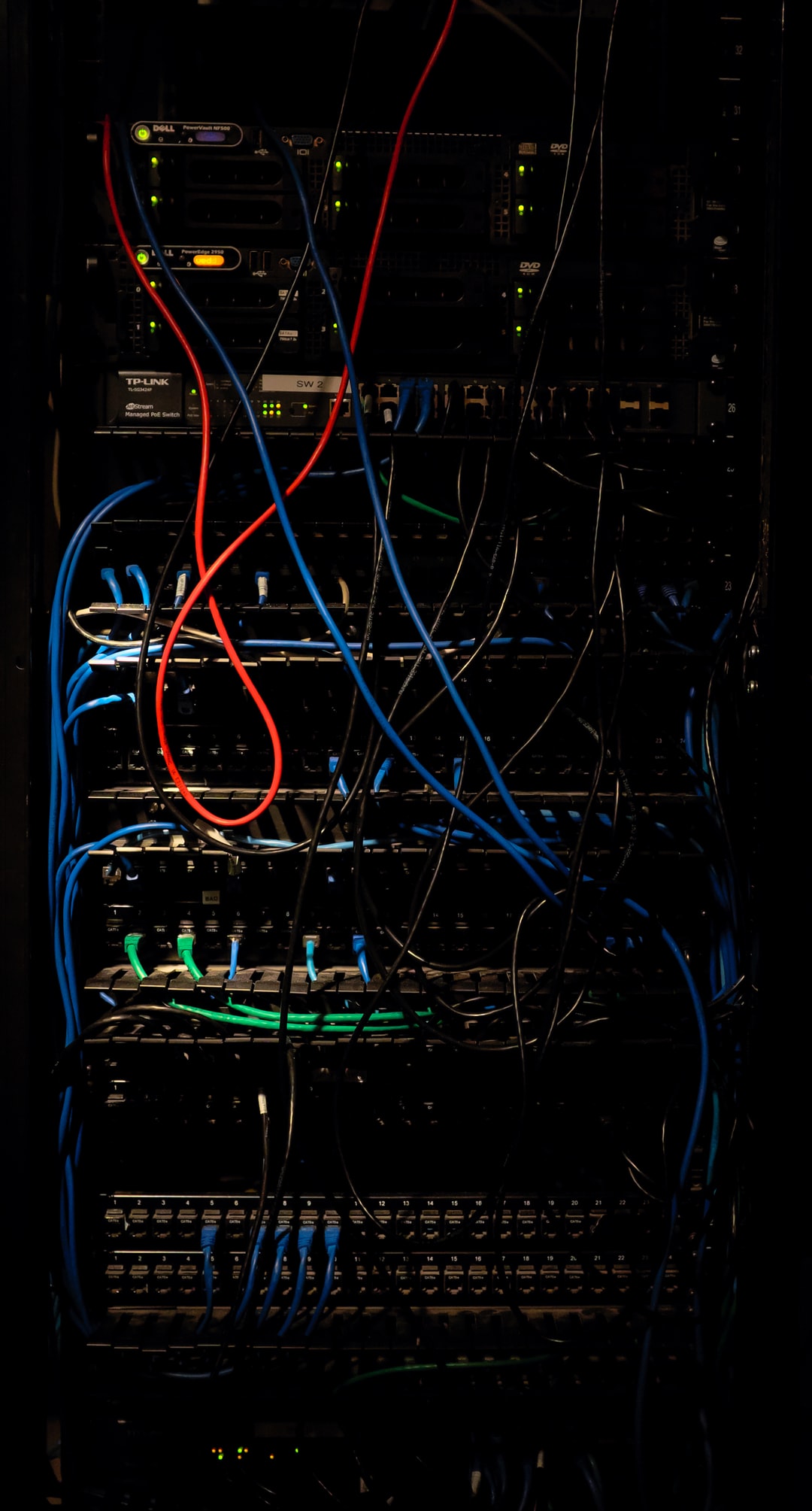
For non-geeks, here is a short introduction. Computer software application contains computer system programs, which give guidelines on just how the hardware ought to perform specific jobs. These softwares are usually prepared by programmers, that have complete accessibility to the entire programs. The programs are then sold to customers with strict guidelines or protocols whereby they are accessible only to particular authorized persons (normally with passwords) for reasons of security. Theoretically, no one other than these authorized persons have access to use these.
How can others acquire unapproved access?
-
The original developers, who have actually prepared the source code, and also have inevitably supplied their own entrance points trap-doors as well as passwords.
-
Earlier individuals that are no longer accredited users, yet whose passwords have not been removed.
-
Various other dishonest persons that want to access the system for ulterior motives.
-
Since there is so much task as well as organization run by computer systems, and the majority of computer systems are connected by the Internet, they are open to be accessed by numerous persons via the internet.
-
Computer systems are additionally vulnerable to strike by harmful software program (mal-ware) and virus assaults, which leaves them open to assault by cyberpunks and mal-ware. These ‘infection infections’ as well as ‘worms’ are introduced by individuals that wish to hack into the system and take information or make entire systems collision or ruin the entire information kept. Just as virus strikes in computers are stopped by anti-virus software program like MacAfee, etc. companies protect themselves from hacking by using honest hackers. EC Council defines an ethical cyberpunk as ‘a person that is generally employed with a company and that can be depended carry out an effort to permeate networks and/or computer system systems using the same approaches and strategies as a malicious cyberpunk.’
It describes the act of situating weak points and susceptabilities of computer as well as details systems by replicating the intent and also actions of malicious users. It is also referred to as penetration testing, intrusion screening, or red teaming. It needs them look at client network as prospective malicious aggressors, after that develop the appropriate safeguards to shield customers from attacks. |
So why are ethical hackers needed?
-
They are required to recognize and also secure all possible points of gain access to by hackers, which can be individuals or innovative software program, consisting of ‘worms’.
-
In basic language, an ethical cyberpunk believes and also functions like an underhanded cyberpunk to discover and also manipulate vulnerabilities as well as weak points in numerous systems, as well as how they can be breached.
-
After that he designs techniques to secure the vulnerable points by setting up firewall programs, stronger passwords, regularly transforming passwords, using iris scans or finger prints along with passwords, encryption, and more.
4 They also need to avoid access (entry) by the initial programmers that developed the software program as well as by persons who are no longer accredited to log into the system.
- They may likewise recommend VPN (Virtual Private Network), a safe passage between a computer system as well as destinations checked out on the net. It uses a VPN web server, which can be located throughout the world, as well as supplies privacy. VPN will do the job to avoid someone snooping your browsing history, or spying on you. VPN will make you browsing from the server geo-location not your computer’s area so we will remain confidential.
With the majority of personal data being offered today online for a price, Information Privacy is a severe concern; hackers can quickly buy your personal data and take your information using your passwords for other websites (because many people have the very same weak passwords for different applications and also rarely change passwords). They will educate customers on how to select hard passwords, where to tape-record or otherwise videotape the passwords, and also how frequently you require to change passwords.
One of the most effective [https://www.jetking.com/] Equipment & Networking Institute in India, Jetking Ltd, an ISO 9001:2008 licensed business, have educated more than 6,00,000 students in the IT sector.

 Never miss a story from us, subscribe to our newsletter
Never miss a story from us, subscribe to our newsletter